Hack Like a Pro: Digital Forensics Using Kali, Part 2 (Acquiring a Hard Drive Image for Analysis) « Null Byte :: WonderHowTo

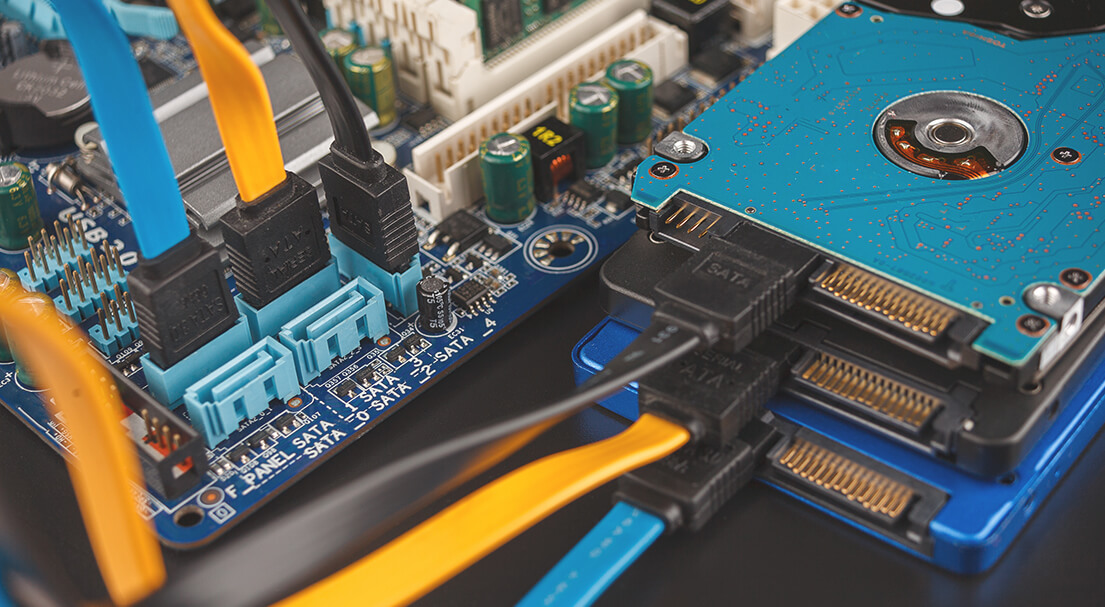
Hack Like a Pro: Digital Forensics Using Kali, Part 2 (Acquiring a Hard Drive Image for Analysis) « Null Byte :: WonderHowTo
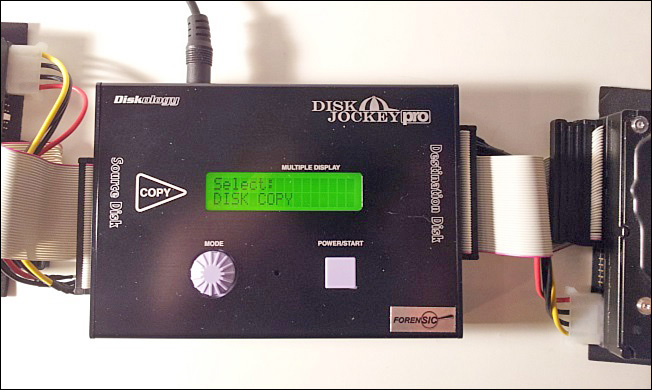
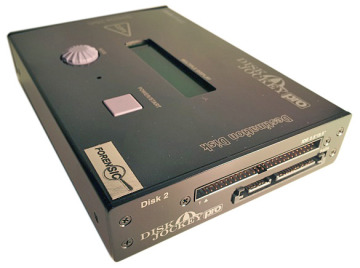
Cloning a PATA or SATA Hard Disk | Handling Computer Hardware in a Computer Forensics Investigation | Pearson IT Certification
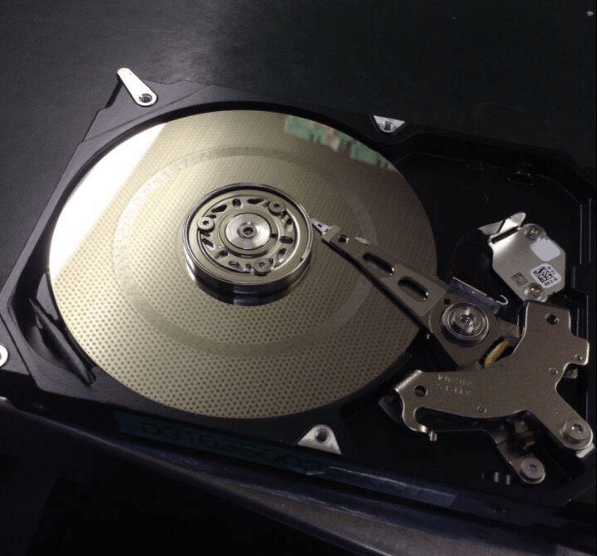
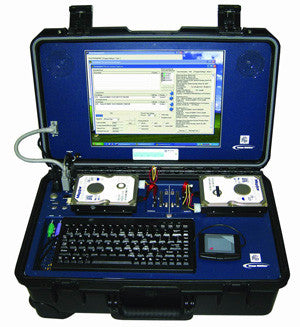
Computer Forensics: Data Recovery & Extraction from Scratched Hard Drives via Salvation DATA Blog | Forensic Files

How to conceal data on a hard disk and dodge (almost) any forensic examination without using encryption or steganography | Hard2bit
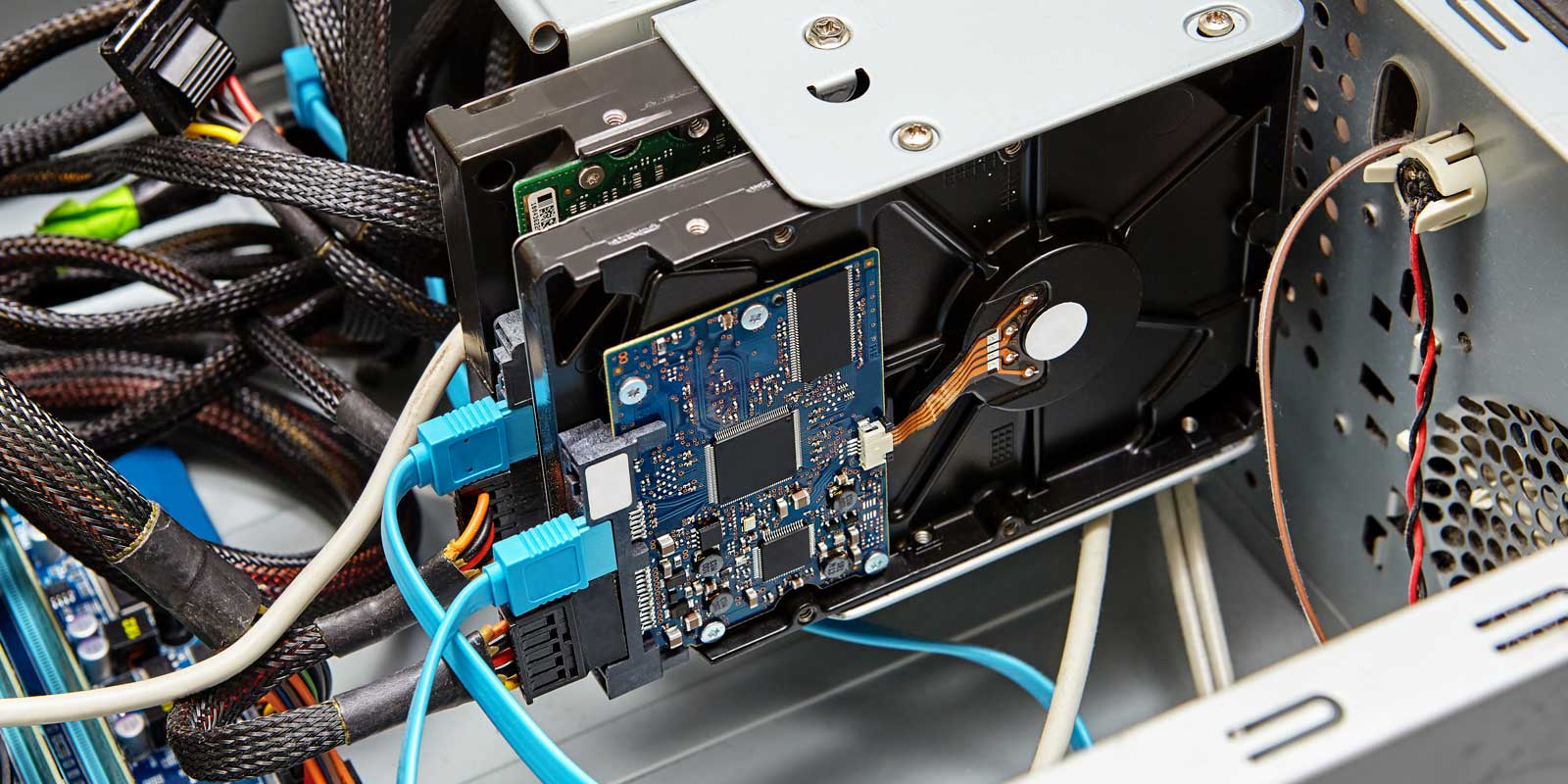
Two Key Differences Between Digital Forensic Imaging And Digital Forensic Clone And How They Can Affect Your Legal Case. | News | CAPSICUM | Digital Forensics, Investigations, Cyber Security